Why do Hackers Hack? Part 2
Could Browser Caching make a difference
to your website conversions – in all honesty
the answer is probably a very simple yes

Chris Pirillo
founder and CEO of LockerGnome, Inc
““Passwords are like underwear: don’t let people see it, change it very often, and you shouldn’t share it with strangers.”“
In 2016, 3 billion Yahoo accounts were hacked in one of the biggest breaches of all time..”
Over the last few months we have increasingly been called to look at websites that have been hacked, compromised, taken over or however you wish to describe it. First of all these are not sites that we have developed or maintain – hopefully that keeps our reputation intact. Every time we talk to clients and potential clients about website security and hacking, the same question comes up – “Why do Hackers hack websites?”
I think that in order to understand why, you need to think about your value to a Hacker and how they can gain from you. This usually, but not exclusively, depends on how big you are or how much data you hold.
If you have not read Part one of this article then I would recommend that you take a look at Why do Hackers hack? Part 1

We have looked at the larger targets on the internet and they look far more enticing than your little website…. Don’t they?
We have looked at the larger targets on the internet and they look far more enticing than your little website…. Don’t they?
That’s very true and if you crack one it is a Jackpot day. However they are probably well protected and you would hope that the likes of Amazon have a very on the ball security team who are spending some of that $7,385 per second to keep our data safe.
So that leaves you, the low hanging fruit for the lower league hacker.
Before we go any further it is probably worth mentioning that these types of attack are less targeted and use automatic tools to scour the internet for vulnerabilities. Let’s think of it a sawn off shotgun as opposed to the sniper rifle approach from my last article. That probably reflects quite accurately the person pulling the trigger. These guys may not even be particularly skilled, simply young kids using pre-written tools – hence the name Script Kiddies
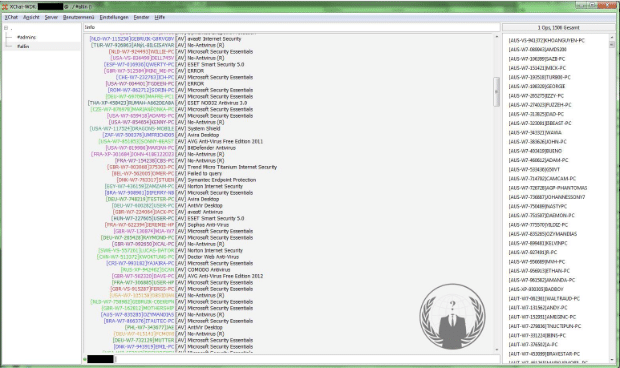
Hacking your individual website probably won’t yield much in the prize stakes but if a hacker can take control of a number of sites then the power he/she has on the internet increases. We are not talking about 2 or 3 sites here but 10’s of thousands
Wham, Bam, Spam
Yes, spam! It’s not from somebody that is sat at their desktop banging away on a keyboard. Oh.no… Spam largely comes from web servers that have been compromised and are doing the hackers bidding like internet Zombies. By sending fewer emails from a large number of servers the hacker can remain under the radar of the authorities. The servers will also act as hosts for the spammers landing pages, spreading their message of cheap pharmaceuticals, bitcoin scams and helping to spread that malicious payload like virus.
DDoS
Large botnets ( Robotised groups of compromised web servers) are commonly used to perform distributed denial-of-service (DDoS) attacks, a way of disrupting a computer system by flooding it with data. Much as with spam, an individual computer in a botnet can’t do much damage on its own, but the combined resources of the entire network enable the hacker to overwhelm the victim server with an enormous amount of traffic.
On parts of the web access to large DDoS botnets is even sold as a “service” to hackers looking to sabotage competitors, take revenge on enemies, or simply make a statement.
Attacking you Visitors
In this instance we are looking at hackers trying to deliver a malicious payload to your sites visitors such as a virus or malware. These are usually disguised as innocent looking links, downloads or updates. Whatever they are they are, looking to propagate their nastiness further
How to keep yourself safe.
The best way to keep your computer and website safe is not to have one in the first place. As that is a bit unrealistic we probably need to look at how we think about security of other things we have and work with. Would you leave your car by the side of the road, unlocked, windows down and the key on the dashboard? No, and I’m glad to hear that. So if we would lock the bad guys out of our car why are we so averse to doing the same with our computers. Here is a simple checklist of things you should have in mind to keep your website and computers safe.
- Have complex passwords – there are plenty of articles on the web as to what a complex password should look like and some tools that will generate them for you.
- Install a Web Application Firewall
- Keep your core website framework (WordPress, Drupal etc) up to date. It’s free.
- Keep all your plugins/extensions up to date.
- Avoid allowing users to upload files to your website.
- Make sure that your web developer/host is keeping things secure.
We provide our clients with a monthly report that outlines what activity has taken place on their site including attempted malicious logins, patching and a list of other things. This means that we are accountable for what happens on their site. It shouldn’t be hard for your developer to provide this kind of information so if you’re not looking after these aspects of your site then make sure they are.
If you are worried that your website may have been compromised then we can help you find out more about how we can help recover your hacked website.
Also feel free to email me at [email protected] and let me know what other articles you would find useful or simply for a chat.